In 2021, we’ve seen the Colonial Pipeline, one of the latest cyber attacks that changed the world, the greatest ever cyberattack in food creation which cursed JBS, the Kaseya ransomware assault by REvil and the Health Service Executive assault on the Irish medical care framework. Such occurrences of cyber attacks ought to remind organizations that, right off the bat, no area is protected from cybercriminals.
One more method to predict what organizations need to plan for on the cybersecurity front in 2022 is to pay attention to the specialists. Information and investigation firm GlobalData for instance reports that “cyber actors will target immature technologies, which means 5G correspondences, savvy urban communities, and the Internet of Things (IoT)”.
In this blog, we have discussed some general cross-sector viewpoints and predictions for 2022 from the cyber threat landscape. Moreover, you can find out the best platform to hire cybersecurity engineers protecting your business from emerging cyber threats 2022.
Table of Contents
Toggle
Table of Contents
ToggleOil and Gas Cybersecurity in 2022
We are seeing the latest cyber attackers take on a style of threats that make a disturbance in human lives. The recent cyber attacks on Colonial Pipeline in mid – 2021 that set off a fuel lack along the U.S. East Coast was just the start. It unfolded that best practice was not consistently followed, even in such an exceptionally regulated area. With the regulatory network (the back office) not isolated from the functional network (the fuel pumping climate), cyber attacks on the regulatory network brought the fuel pumping network into danger and end up being closed down to protect it – influencing generally 45% of the Eastern Sea Board fuel supplies for nearly a week.
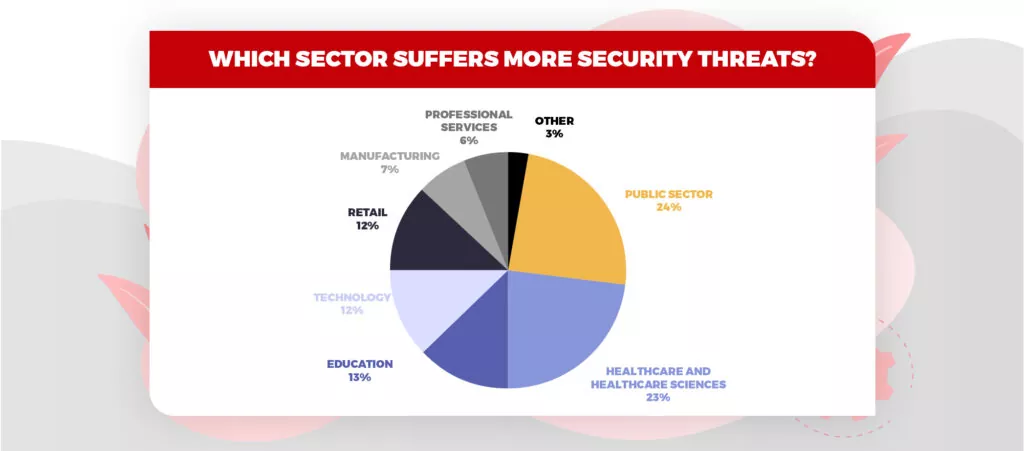
Image Source: Itgovernance
Transport Cybersecurity
Big data and 5G will invite new vulnerabilities. The worldwide rollout of 5G and more and more usage of smart vehicles containing a symphony of sensors is now producing a huge amount of data about users’ likes and dislikes. Data collected from these sensors help manufacturers understand the behavior of customers and accordingly work on improvisation.
As smart vehicles usage is in prevalence, we can anticipate that cyber actors may focus more on vehicles. We might even see the reemerging of a modern day ‘digital Dick Turpin, copying the seventeenth-century highway burglar requesting money for travel.
Also Read – Is Your Company Following these Cyber Risk Mitigation Strategies?
Aerospace Cybersecurity
We can hope to see new proof-of-concept (POC) attacks focusing on satellite networks in the coming years as satellite-based web access keeps on developing. The greatest targets will be organizations that depend on the satellite-based networks to help low-latency activities, as internet gaming or delivering services to remote areas, just as remote field workplaces, pipelines, or travels and aircraft.
“This will likewise grow the attack surface as organizations add satellite organizations to interface already off-grid frameworks, like far off OT gadgets, to their interconnected networks. In a huge number, Linux runs the back-end figuring frameworks, and as of not long ago, it has not been an essential objective of the cybercriminal local area, yet we expect this to get in 2022.”
Automotive Cybersecurity
2021 was the extended period of cybersecurity guidelines for the automotive business. Automotive SPICE for Cybersecurity, and TR-68:3 ‘Autonomous vehicles: Cybersecurity standards and evaluation structure’ were totally delivered. ISO/SAE 21434 ‘Road vehicles: Cybersecurity engineering. The ‘OpenChain ISO 5230 – Security Assurance Reference Guide 1.0’ focusing on security for open source programming was additionally released.
“In 2022 we will see a proceeded adoption of these guidelines and specialized references among automotive companies. We can likewise expect streamlined workflows based on further developed security mindfulness in the associations, relevant security training for product groups, and expanded utilization of rules, layouts, and mechanized security testing instruments for playing out the necessary network safety exercises.”
Benefits of Contract Staffing Services
Logistics Cybersecurity
The roaring logistic sector will be perhaps the most alluring target for the cyber actors in 2022, and worryingly, may likewise be one of the most unprepared sectors. A greater part of logistics organizations doesn’t have a chief information officer, which demonstrates that network protection isn’t fundamentally important in the area.
In 2022, we’ll see logistic organizations making a similar degree of transparency in their digital guards as they implement them in their production network tasks. This will be driven partially by strain from external stakeholders with the liability regarding guaranteeing streamline of operations in this area – be that financial backers, investors, or clients.
Healthcare Cybersecurity
Indeed, even before the pandemic struck, the healthcare industry had been encountering a great development in the number of associated devices used to give care and manage facilities. With the huge expansion in ransomware attacks against medical care frameworks seen in 2021, we can securely anticipate a much bigger expansion in 2022.
“These cybersecurity attacks will probably move from simple yet risky ransomware encryption of data – like the overwhelming WannaCry attack that impacted large parts of the NHS in 2017 – to holding hostages associated clinical gadgets with a denial of service attack on top of the information encryption. The extended cybersecurity attacks surface will carry with it new compliance mandates protecting more gadgets on the clinic organization.
Finance and Fintech Cybersecurity
Financial institutions have been progressively dependent on voice examination as a safety effort and threat actors community has as of now cottoned on. This technique was utilized effectively at the end of the year 2021. Banks and global investment houses need to observe and guarantee their security strategies are not over-dependent on any single innovation arrangement.
Cryptographic trades and wallets can contain huge wealth that can be an extraordinary bait to cyber attackers hoping to benefit from their assaults. In 2021, there has been an increase in the number of cyber attacks connected with cryptographic forms of money. In recent cyber attacks, these were simple social engineering assaults, and some of them were technically advanced.
Also Read – Is Artificial Intelligence (AI) the Future of Cyber Security?
Retail and eCommerce Cybersecurity
“As retailers keep on pushing the envelope with customer commitment with Augmented Reality and Artificial Intelligence, different types of information are additionally being gathered and new cybersecurity concerns arise. For example – virtual fitting rooms to take a try at garments. They make a new digital actual reality where biometric information is needed. This helps in expanding the platform for cyber attacks and gives freedom for cyber actors, and it is certain that these frameworks will be focused on by cybercriminals.
Now you must have understood that cyber actors are trying their luck in each and every sector. Therefore, it won’t be fair to say which sector is more vulnerable. Instead, CEOs of every sector must learn from recent cyber attacks and have a proper strategy and plan on how to react to unprecedented cybersecurity attacks.
Haven’t you formed a cybersecurity team yet? If not, PeoplActive can help you hire experienced cybersecurity experts working towards your business cybersecurity. Leverage our pre-vetted talent pool of cloud cyber security professionals and hire a team or an individual within 48 hours. Let us know your requisitions!