Almost every organization has migrated to the cloud to varying degrees within their business. Haven’t you yet? Although one reaps multiple benefits by operating on the Cloud, however, it welcomes security threats too. As cloud security threats continue to evolve, one must be very stringent while structuring the cloud security team and roles. In this blog, we will be discussing several aspects of cloud computing security and much more, so stay tuned….
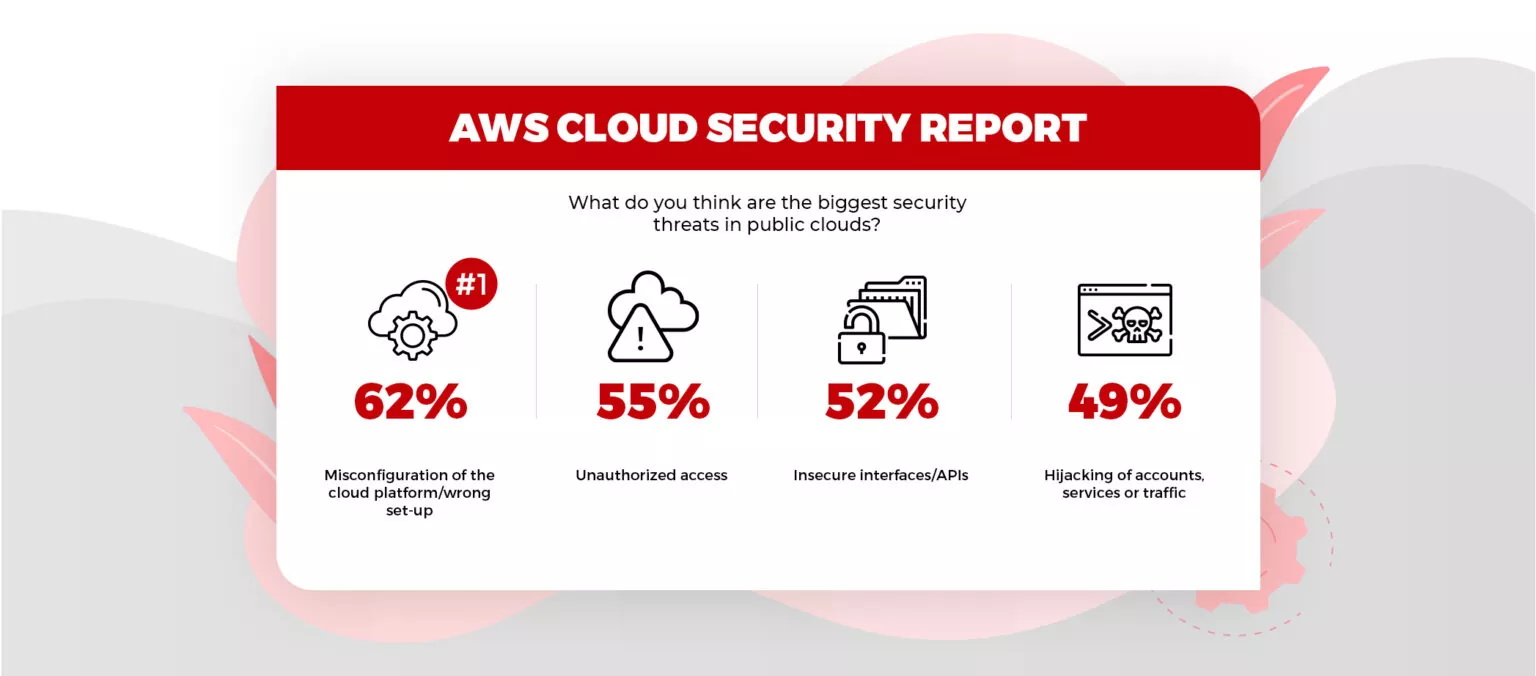
Table of Contents
Toggle
Table of Contents
ToggleIs Cloud Computing Secure?
Before migrating data to the cloud, it’s natural to ask if cloud computing is secure. Actually, on closer inspection, you will realize that it’s not the cloud at fault but the people using it. Most of the cloud security failures happen due to user error—typically poor password management (i.e. Uber), misconfigured databases (i.e. Hova Health), improper access controls (i.e. Time Warner Cable), unsecured storage buckets (i.e. Accenture), etc. The data you save with cloud service providers is safer than the data you’ve stored in your computer’s hard drive. Hackers can use malware to freeze your computer and phishing emails demanding a ransom to release information they’ve frozen. The security measures undertaken by cloud service providers are more robust and powerful than what you have protecting your home computer and devices.
That is why every organization should hire a great security team who can protect business data and maintain data integrity.
Types of Cloud Security Threats
More and more data is being deployed to the cloud which creates unique info security challenges. You must have heard of several cloud data breaches that have exposed sensitive data. Below are the widespread types of cloud security threats that hackers use.
Malware
Malicious programming where harmful components are veiled as genuine documents. This incorporates different sorts of viruses, spyware, Trojans, worms, and so on.
Ransomware
A malware type that works by locking the victim’s framework documents under encryption and requesting a lot of money to open them.
Phishing
A strategy of sending emails resembling credible messages, yet containing harmful links that contaminate your PC with malware and attempt to take your credit card subtleties or banking account login data.
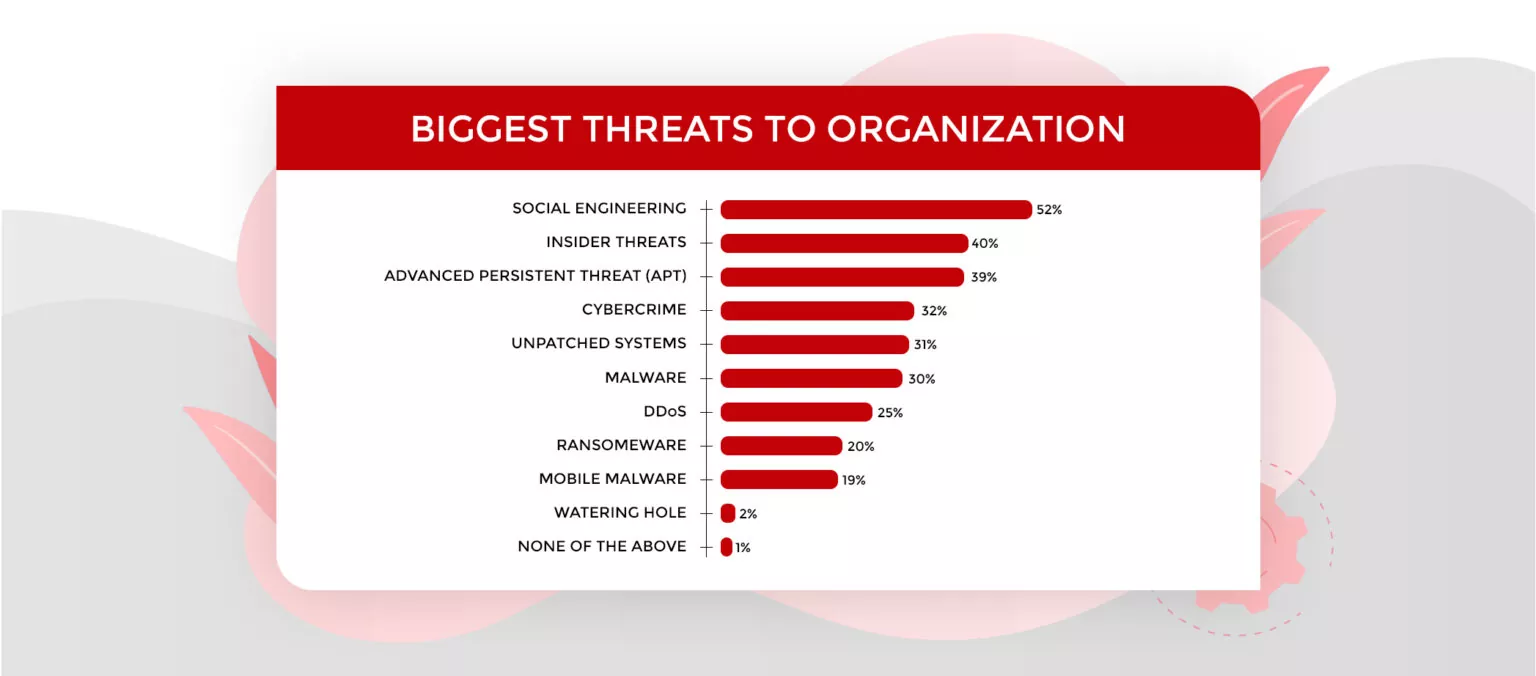
Social Engineering
We are utilizing social relations to acquire the trust of a victim and compel it to give admittance to sensitive data.
The Ultimate Guide To Cloud Cost Optimization
Types of Cloud Security Threats
There are numerous physical security hazard factors, alleged danger vectors — means or ways for a programmer to access your ensured frameworks. There are numerous assortments of danger vectors, the most well-known being as per the following:
- USB sticks, micro SD cards, and other compact data storage gadgets
- Browser extension of unclear origin
- Infected sites
- Malicious commercials
- unused web-based media accounts
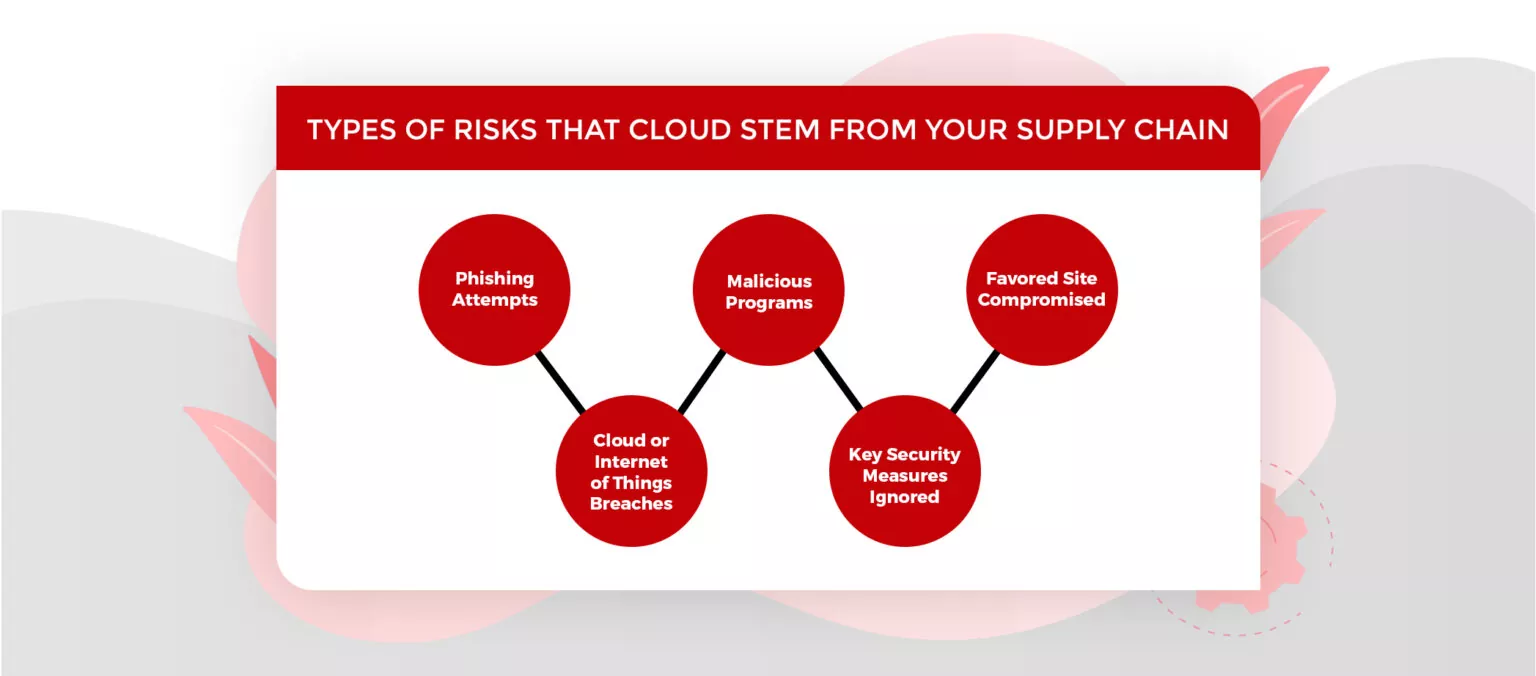
- Online tests and personality surveys
Your vendors can also expose your organization to new cybersecurity risks. Therefore, ask your security team to evaluate the vendors and the potential risk they can bring to the organization. Create a security policy to address the risk and the action plan to pursue in your vendor doesn’t address any security concerns.
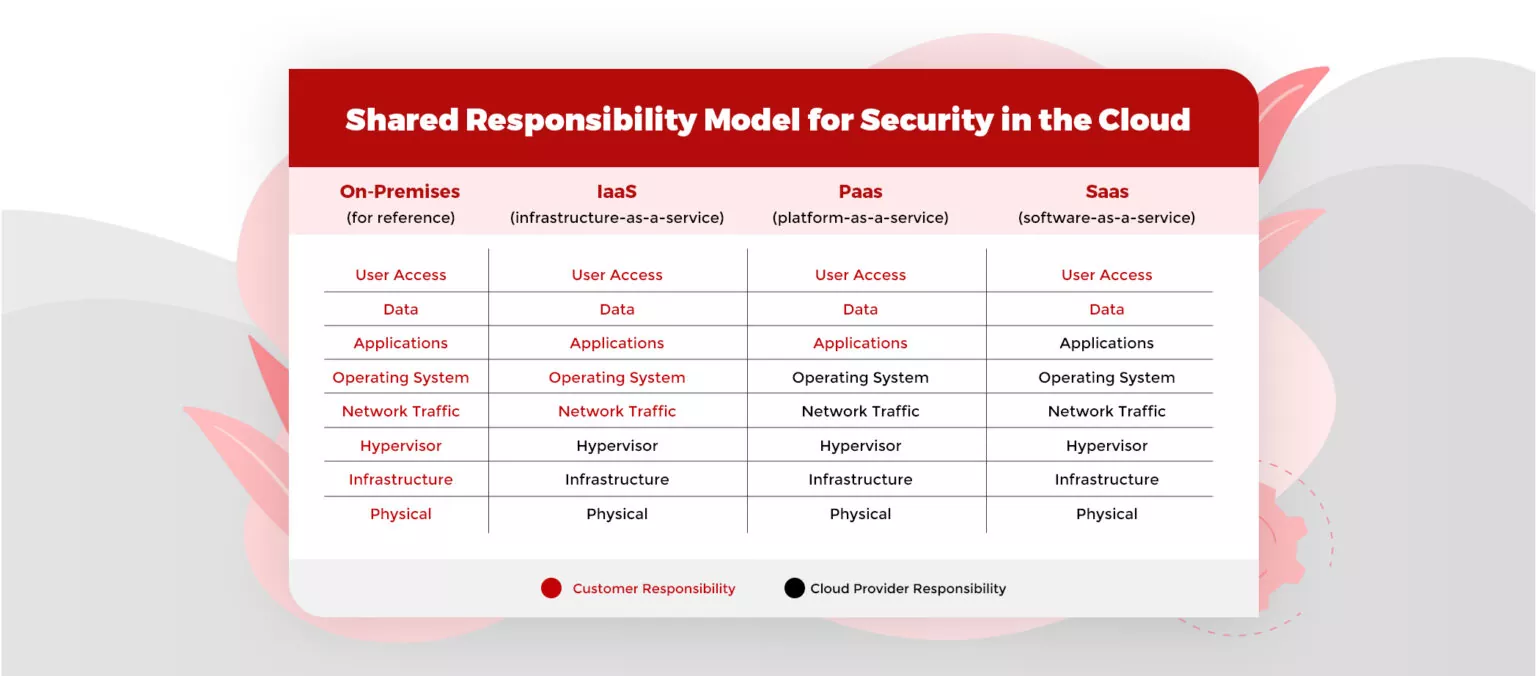
Cloud Security Checklist
Cloud migration comes with a new set of security concerns than a traditional environment. Having a cloud security checklist at every level protects you from several attacks and data breaches. Remember, a small security carelessness at a lower level (for eg. Improper policies and procedures of the company) in the enterprise can lead to a major loss. Implementation of security checklist items may differ as per the organization’s unique environment, however, the principles remain as it is regardless of their implementation. The responsibility of the security system is on the shoulders of both the cloud provider and the client.
1. Policies and Procedures
In a survey, Gartner has estimated that “through 2022, almost 95% of cloud security breaches will happen due to the customer’s fault. Below are some checklists on the company’s policies and procedures that will help in eliminating threats.
- Have all security strategies and techniques been refreshed to incorporate the cloud?
- Are security techniques set up for onboarding workers?
- Are techniques set up when workers leave or change jobs?
- Do you have techniques to manage any security infringement?
2. Access Management
This is an initial phase in getting your cloud environment secure. This controls how to recognize and confirm clients, just as who can allot access rights. In 2016, Forrester assessed that “80% of safety breaks included privileged credentials”.
- Who has access to your system? Are they suitably checked?
- Does every one of your workers has trained in security awareness?
- Are you using multi-factor authentication?
3. Networking
Utilizing a cloud-based environment puts an obligation regarding the organization’s security on the cloud supplier. Being a customer, you need to inquire:
- Are there gateway safety measures against malware threats?
- Are there safety measures against network-based attacks? Disabling RDP access from the web and limiting web SSH and SQL Server access will prevent attacks on VMs.
- Is all confidential material encrypted over strong networks?
4. Back-Up and Data Recovery
There are several ways that can cause data loss such as hardware failure, malicious action, and natural disaster. It is very important to have a data recovery plan to stay away from devastating data loss. Before choosing the cloud service provider, you should ask –
- Do they have backup and data recovery plans and procedures?
- Do they embrace regular testing to guarantee full data restoration
5. Security Patches and Updates
Keeping your systems refreshed with the most recent security patches holds the utmost importance. Ask yourself:
- Have you installed the most recent security patches?
- Have you tested the security patches on a development level before deploying them to live servers?
- Do you consistently check your framework weaknesses?
6. Data Encryption
Encryption guarantees that in case your data is breached, as long as the keys are secure it is futile to the hacker. The more sensitive the data is, the more significant it is to get with encryption. For that, you have to ensure –
- All confidential data kept in servers or transit must be encrypted.
- Safeguard all private keys and public keys
Cloud Security Team Structure, Size, and Roles
There are several key job roles that should be included in any cybersecurity team irrespective of its size. It may be difficult for small-scale companies to hire full-scale cloud security IT teams, nor should they. In case you run a relatively smaller company, a single cloud security specialist expert, in-house or outsourced is sufficient to fill in every one of the job roles listed below.
- CISO or Chief Information Security Officer – A member who is responsible for examining the current and future cloud security demands and planning an organization security technique and guide, just as supervising the tasks of your cloud security IT team and authorizing the necessary changes across the organization.
- Cloud Security Architect – A member who is liable for designing and executing the security work processes, incident reaction situations, policies, and guidelines. As this position requires both technical background and a deep understanding of the business measures, this is a critical job role in guaranteeing the cloud security measures stay lined up with the overall business development system.
- Cloud Security engineer – An individual liable for taking care of day-by-day security activities and checking the presentation of your IT framework.
- Security Auditor – An individual responsible for streamlining your cybersecurity routine, as this expert attempts to bypass your safeguards as any hacker would, thus distinguishing possible risks, so that team can respond and eliminate them proactively.
Also Read: Important Factors to Consider Before Hiring Candidates
The cloud security team structure and size differ based on the extent of work. There can be multiple Cloud Security engineers, Cloud security architects, analysts, a team lead, and a project manager. It won’t be easy to fill these job roles with top-notch professionals urgently or in a short period, however, with the help of staffing agencies you can definitely do so.
Hiring Cloud Security Professionals from PeoplActive
High-performing security teams very well know their individual roles, also, they work together to defend against adversaries. Organizations should prioritize where to invest based on the risk profiles, needs, and resources. Hire the best cloud security professionals and keep your data safe and secure. PeoplActive is a global staffing agency that delivers remote talents for cloud security roles to its clients helping them process their data on the cloud. Our team has been recruiting and staffing candidates having good years of work experience in AWS cloud security/Azure security/GCP security as well Hybrid Cloud. Which one do you need?