The development of electronic healthcare records, telemedicine and inter-connected medical devices showcases how technology has penetrated healthcare. It has greatly expanded the field of patient care and patient management. As per a KPMG report, the medical device industry is projected to reach $800 million by 2030. Despite its growth, this industry is also facing threats from cyber-attacks and data breaches.
Imagine what would happen if cyber attackers get unauthorized access to medical records? Changing patient data, causing downtime in healthcare operations, and manipulating medical devices are all possible. This can impact the quality of care and even loss of trust in the healthcare institute. All these daunting scenarios highlight the need for robust healthcare cybersecurity measures. This blog explores what cybersecurity measures healthcare organizations need to take to protect patient data and how cybersecurity consulting services can help.
How Has Cybercrime Impacted the Healthcare and Medical Industry?
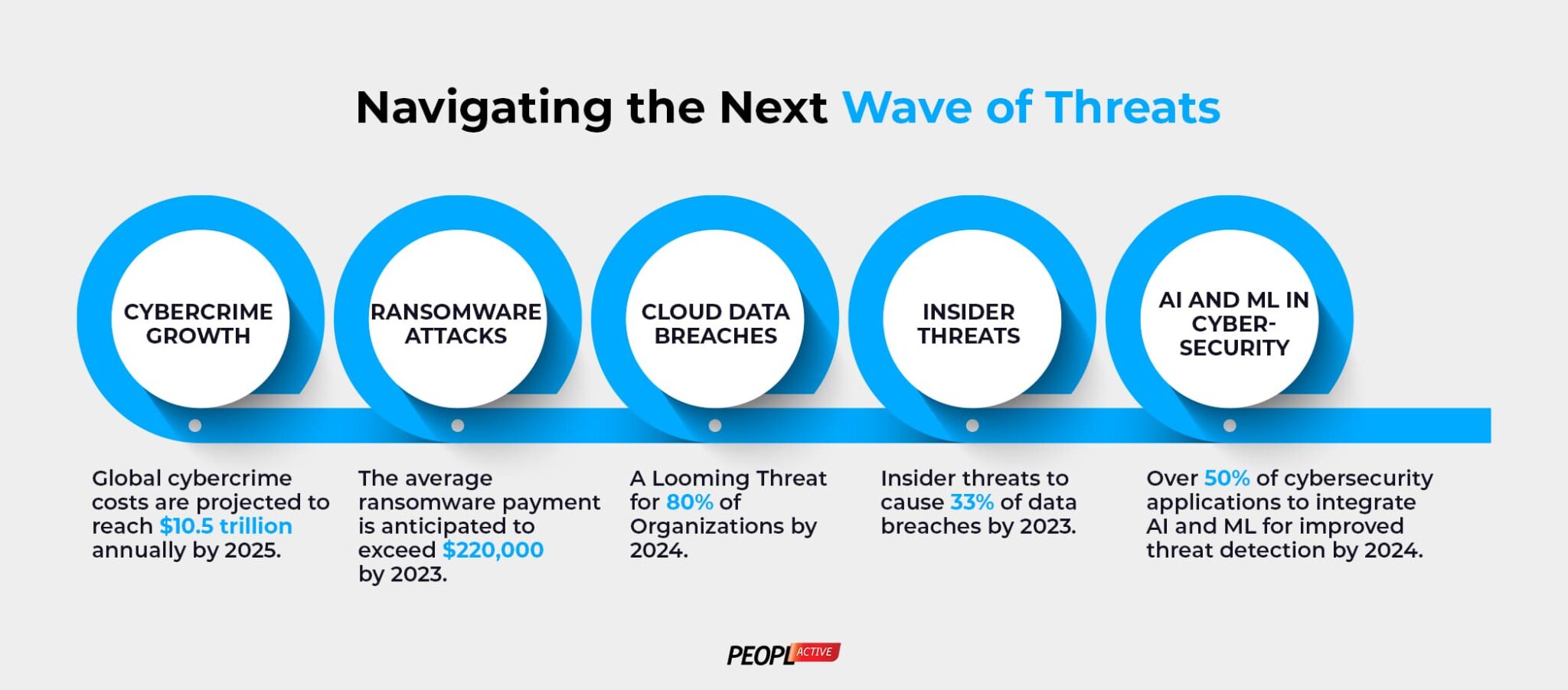
Cyber-attacks have evolved to not only endanger the financial health of healthcare organizations but unauthorized access to medical devices can also lead to misdiagnosis, incorrect treatment plans, or delayed care. In some extreme cases even patients’ lives are at danger too. To paint a clearer picture of this, in 2023 993 vulnerabilities were found in 966 healthcare devices tested, a 59% increase in the vulnerabilities which can be exploited by attackers to target healthcare organizations.
The recent attack on a hospital in London showcases an example how cyber attackers infiltrated the hospital’s systems and disrupted the operations. As a result, a lot of the critical operations had to be cancelled because medical records of patients were stolen. This also demonstrates that hospitals are unprepared or don’t have a vulnerability management strategy against cyber-attacks. To put this thing across as numbers, only 28% organizations globally take a proactive approach to secure their medical devices from such cyber incidents. Furthermore, it also comes down to financial consequences, legal fines and reputational damage in the long run. All in all, this boils down that healthcare needs to take more robust steps to safeguard patient data and their medical devices.
How to Protect Patient Data?
Now, that we have seen the seriousness of cybercrime in patient welfare and data, here are five steps that cybersecurity consulting services advice to take to protect patient data:
1. Encrypting Data:
In many cybersecurity regulatory compliances, data encryption is a requirement, preventing unauthorized users from intercepting data. To secure Protected Health Information (PHI) especially on electronic devices or connected devices, healthcare companies need to encrypt data not only when it is at rest but also when in transit. Similarly, e-mails containing sensitive information should also be encrypted to prevent data theft. Strong encryption standards such as AES-256 can be used for data encryption.
2. Access Controls:
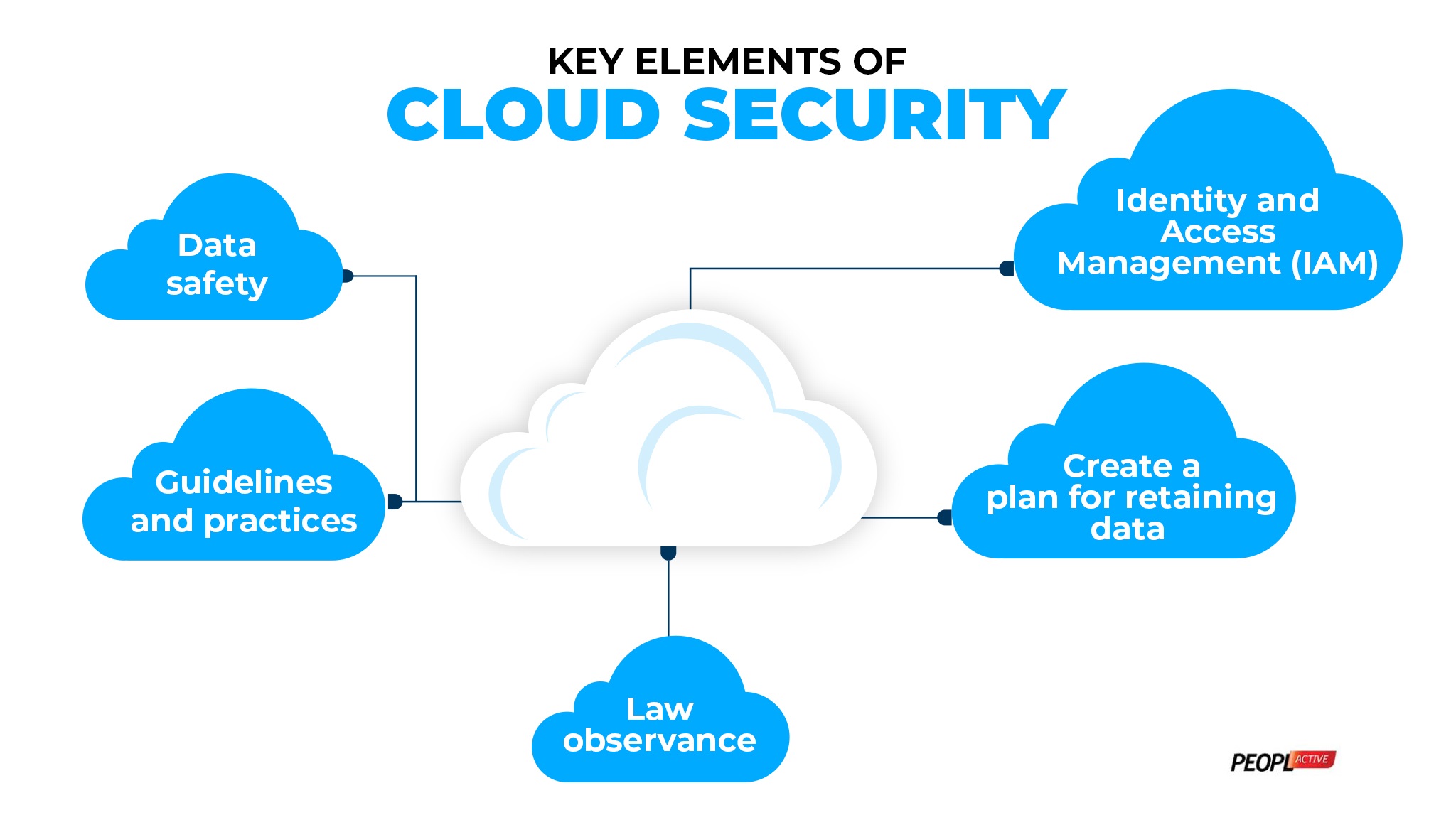
Patient information should not be accessible to everyone in the organisation since internal theft is a common cybercrime. By implementing security controls like role-based access controls and Multi-Factor Authentication (MFA) can reduce unauthorized access of data. With role-based access controls organizations can define access based on the professional’s role. Furthermore, MFA adds an extra layer of data protection security. Putting in place a security policy can further amplify healthcare data security.
3. Patch Management and Updates:
78% of healthcare professionals worldwide say that patching vulnerabilities in medical devices is the biggest gap in their defenses. Every IT team dread updating software, and it is easy to see why. Keeping each piece of technology updated and secured is often time-consuming. But regular updates protect the device and the critical information it carries by patching the vulnerabilities before they are exploited. Healthcare professionals can follow a practice to test the patches in a controlled environment before deploying them to ensure proper functionality.
4. Backup Your Systems:
Backup standards usually require encrypted data, including PHI and PII. Taking such a precaution is important to guarantee that the data is backed up in a timely and right manner. The healthcare company has a choice between full backups, incremental backups, and differential backup in accordance with their health records requirements.
Backup standards usually require encrypted data, including PHI and PII. Taking such a precaution is important to guarantee that the data is backed up in a timely and right manner. The healthcare company has a choice between full backups, incremental backups, and differential backup in accordance with their health records requirements.
It is a prerequisite to carry out security assessment, such as third-party risk assessments or timely security audits to find appropriate ways to protect your patients’ health information. Security audits help healthcare organizations in multiple ways. They can find out whether or not vendors comply with the same cybersecurity standards. Furthermore, it gives them an idea of their security posture as they learn their vulnerabilities. By regular audits they can stay vigilant and detect any abnormalities before they escalate.
The healthcare company can choose to employ cybersecurity consulting services to aid in protecting sensitive patient information and implementing necessary measures to safeguard data and medical devices.
How to Protect Medical Devices?
As medical devices get more connected so does the attack surface area that exploits their vulnerabilities. Ensuring their security not only ensures care continuity but also the integrity of medical treatments and the trust in healthcare providers. Furthermore, healthcare providers must invest in secure medical devices to avoid cyber incidents. Here are a few ways that healthcare cybersecurity consulting companies would advise you to take care of:
1. Risk Assessment:
A healthcare cybersecurity consulting company will test and probe medical devices for potential threats and weaknesses. If vulnerabilities and compromises are found, they should be rectified immediately. These assessments are done in context with the types of vulnerabilities in medical devices which are categorized based on hardware vulnerabilities, software vulnerabilities and OS vulnerabilities. Once these are identified then with proper security updates these vulnerabilities can be eliminated.
2. Network Segmentation:
Through isolation of medical devices from the standard production network, the other medical devices are protected from becoming contaminated. Medical devices can be placed on a separate network which enables hospital to avoid the risk that a system which accesses less secure websites could infect a mission-critical device.
3. Incident Response Plan:
An incident response plan for medical device compromise should include the following steps:
- Identify and report the incident
- Evaluate its severity and inform the appropriate team
- Address vulnerabilities and reduce impact
- Resolve the incident and conduct a post-incident analysis
- Update, improve and test the plan
This plan helps healthcare organizations effectively respond to medical device compromises and minimize the impact of cyber incidents.
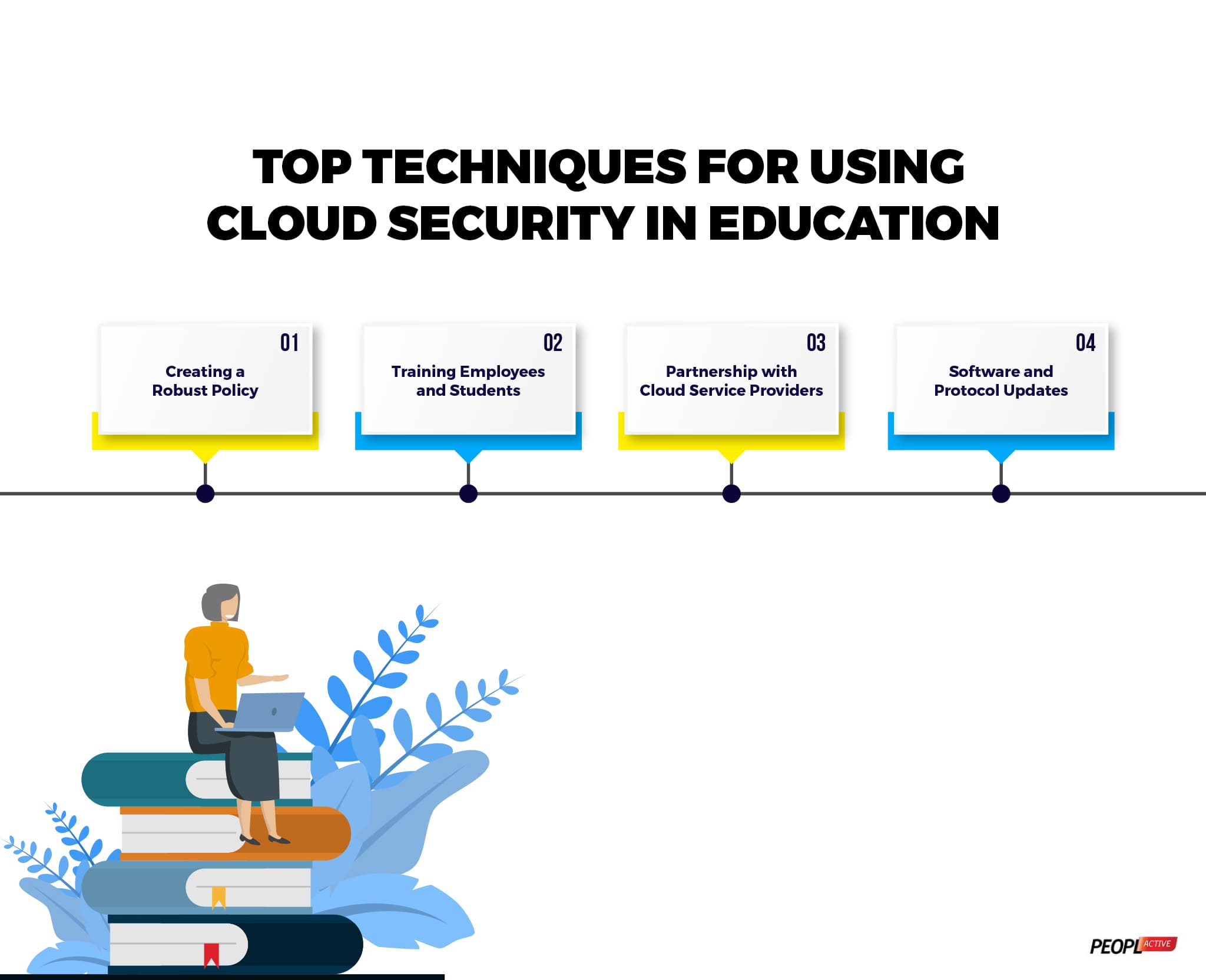
4. Staff Awareness and Training:
Without any knowledge, the healthcare staff could download a contaminated file, run unauthorized software, or plug in a corrupted pen drive. Train staff to create strong, secure passwords and change them regularly in adherence with the compliance policies. By training staff who are engaged with medical devices, the hospital can create a secure environment and a new line of cyber defence.
5. Secure Software Development:
Integrating secure development practices like encryption protocols, secure operating systems, access controls in the medical device product development stage can minimize the risk of cyber threats. By adhering to the compliance standards created by international bodies for medical device development and practices like secure by design can further strengthen the resilience of medical devices. Finally, updating the devices and patching the device for vulnerabilities can improve the device’s security in the long run.
How to Move Forward
The rise of interconnected devices makes room for both opportunities and risks which is why cybersecurity measures to protect patient safety, privacy, and health system security must be a top priority. Regulatory bodies and standards organizations have brought guidelines and compliance standards which must be adhered to deal with such incidents, giving reference to manage medical device cybersecurity and minimizing the threats.
The healthcare sector experienced many data breaches, indicating need for the comprehensive cybersecurity plans and practices. Making and enforcing these plans and practices standalone is a difficult task for a healthcare company. Not to worry, PeoplActive is here to assist your organization to achieve complete cyber resilience. With a team of dedicated cybersecurity experts who have years of experience and expertise of the best cybersecurity practices, you should partner with us for a safer tomorrow. Learn more about our healthcare cybersecurity consulting services to build cyber resilience for your healthcare business.