Do you really need Kubernetes? What does Kubernetes(k8s) do, Anyway? Organizations are embracing the concept of microservices and containerization to develop applications faster and in more secure environments. Nothing can better manage containers than Kubernetes. Let’s find out what Kubernetes is, Kubernetes security checklist, benefits of Kubernetes, cloud container security checklist, and more.
Table of Contents
ToggleWhat is Kubernetes?
Kubernetes is an open-source platform used to automate the containerized workload management. It automates the load balancing, manages service discovery, tracks resource allocation, and several other activities required for automatic containers deployment. Click here to find more about Kubernetes benefits.
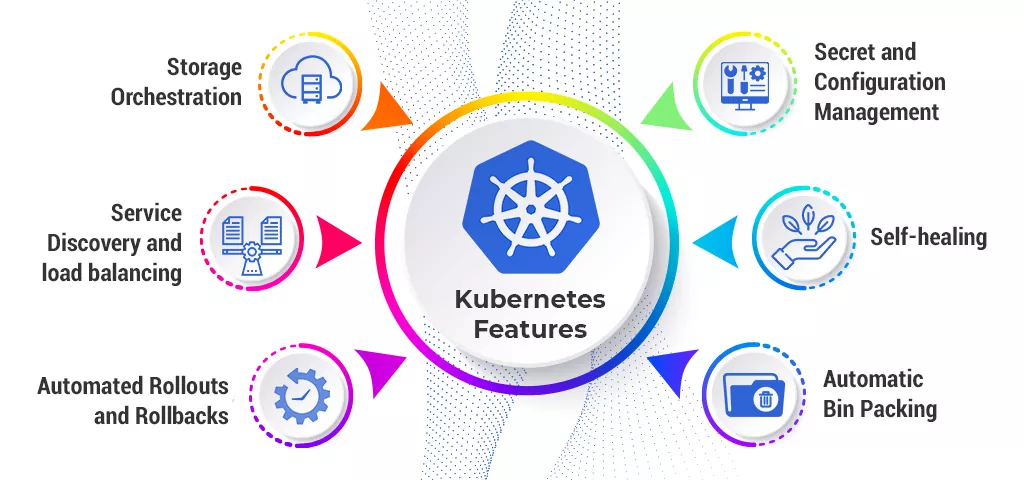
Benefits of Kubernetes –
- Portability and flexibility
- Multi-cloud capability
- Increased developer productivity
- Reduce cloud complexity
- Open source
What are Containers?
A container is an independent unit that contains code and all its dependencies together so the application can run quickly from one computing environment to another. But there is a cloud container security checklist that must be followed during the SDLC. We will explore those cloud container security points under the Kubernetes security guidelines later in this blog.
Benefits of Containers –
- Less overhead: Containers require fewer resources as compared to the traditional environments since they do exclude operating system images.
- Expanded portability: Applications running in containers can be deployed effectively to different OS and hardware platforms.
- More reliable operation: Groups of devops engineers know applications in containers will run in the same manner, irrespective of the platform they are deployed.
- Better productivity: Containers permit applications to be all the more quickly deployed, fixed or scaled.
- Better application development: Containers support agile and DevOps endeavors to speed up development, test, and production cycles.
Also Read – Cyberattacks Are Inevitable. Is Your Company’s Cloud Storage Secure?
Kubernetes security checklist can be defined along 4 areas:
- Infrastructure
- Kubernetes
- Containers
- Applications
1. Infrastructure

Infrastructure level security is the basic yet the biggest thing to consider while developing an application. There are several factors that come under the infrastructure dimension. Let’s find more on this Kubernetes security checklist –
Networking
In Kubernetes, usually deployment is microservices, where all the microservices are communicating with one another or external applications. Therefore, it becomes imperative to limit the networking traffic and allow only what is useful. Networks should have lower-level access control at the hardware level and better control over the traffic in a shared environment. Here, you will consider the different aspects of network design to foster a protected and secure network. Explore what are specific guidelines under Kubernetes security checklist to protect network.
- Isolation of control traffic – Isolating Kubernetes control-plane traffic from data-plane traffic helps avoid traffic overshadows which may cause temporary service disruption. This one of the Kubernetes security best practices.
- Isolation of Storage traffic – There are chances that the infrastructure’s storage service may bring down the application network. To avoid that, organizations isolate storage traffic from regular data and control traffic.
- Network Segmentation – Kubernetes hides the basic framework from users. Developers should keep this fact in mind while designing the network. Networking infrastructure should support both Layer 2 VLAN-based segmentation and Layer 3 VXLAN-based segmentation, to segregate the traffic between different tenants or applications.
Also read: Azure Firewall Architecture
Kubernetes VS Docker - Which to Adopt ?
Storage
Storage is more vulnerable to cyber-attacks. Developers working on Kubernetes must implement below-given Kubernetes security checklist at the storage level.- Self Encrypting Drives: With these drives, encryption is offloaded to the disk itself. This guarantees that in the event that somebody gets physical admittance to the disk, data won’t be accessible to them. This is among Kubernetes security best practices followed by engineers.
- Volume encryption: In a shared infrastructure, Kubernetes CSI deals with the lifecycle of the volume. This detaches the users from the hidden storage. Volume Encryption guarantees that individual volumes are secure against undesired access.
- Quality of Service: In a shared infrastructure, I/O-heavy application may affect the efficiency of other applications. Therefore, the underlying storage infrastructure must have the capability to ensure a guaranteed service level to each tenant.
Host and Operating System
The next level of security practice in Infrastructure is the physical or virtual host itself. Engineers can secure the underlying foundation in different ways –
- Enable Kernel Security – Enable security modules like AppArmor and SELinux to limit access to the applications, processes, and files in a system.
- Audit Logging – Implementing audit logging helps in monitoring systems, debugging, and finding the security beaches.
- Rotate Credentials – It is one of the best practices to rotate the user credentials frequently to avoid security breaches.
- CIS Conformance Test – This test is done to ensure that all the security practices have been implemented successfully.
- Lockdown the Nodes – All the nodes must be lockdown after they are provisioned and set up in the Kubernetes cluster.
Read more: Green Cloud Computing Architecture
2. Securing Kubernetes

After securing the infrastructure, the next level to secure is the Kubernetes installment process. In an open-source Kubernetes installation, there are many settings that need to be done manually as they are not on by default. Let find more on this second most important Kubernetes security checklist –
Secure etcd
etcd is a key-value store used as a backing store for cluster data in Kubernetes. It stores all states and secret data of Kubernetes which makes it very important.
- Lockdown nodes within etcd with minimal access and must be Accessible to masters only.
- Encrypt the drives containing the etcd data.
- Ideally, etcd communication should be over TLS.
Securing Access to Kubernetes
Kubernetes offers access control solutions to secure the data. These can be broken down into the following Kubernetes security best practices as listed below.
- Authentication – Kubernetes has several authentication modules: Client Certificates, Plain Tokens, Bootstrap Tokens, Passwords, and JWT Tokens. For production environments, enterprises will require an external user management and authentication plugin that supports these capabilities.
- Authorization – Once users are connected to the Kubernetes cluster, it is important to authorize them for accessing the requested resources. Kubernetes supports multiple authorization modules including ABAC (attribute-based access control), RBAC (role-based access control), and webhooks.
- Admission Control – It is used to intercept and control the Kubernetes requests and allows users to access only if they are authenticated and authorized.
Security Policies
Kubernetes provides few configurable policies which need to be aligned as per enterprise practices. They are not set by default but need to be defined by the users. Check out what are those practices in Kubernetes security framework.
- Pod Security Policy – an admission control plugin to ensure that pods are admitted only when certain security guidelines are met.
- Network Policies – By default, the pods are non-isolated. Therefore, it is important to set network policies to control the group of pods and communication between them.
- Quality of Service – To guarantee that enough computing resources are provided to avoid noisy neighbors and starvation problems.
Also Read – Must-Have Steps in a Cloud Migration Checklist
3. Securing Containers
Containers need to be secured in both phases – while they are being developed and while they are running. Check out the key elements under this cloud container security checklist-
Container Image Security
The containers are based on an image file that is downloadable from an open library or can also be passed from one team to another. Team members should keep a track of where these images are coming from and what’s inside them. Let’s find what comes under this particular cloud container security checklist –
- Image Vulnerability Scanning – Container images must be scanned using tools like Aqua, Twistlock, Clair, etc to detect the known vulnerabilities. These tools scan all the packages and dependencies in the image and find out the vulnerabilities.
- Image Signing – Enterprises need to strictly admit images that are only signed via corporate Notary and maintaining a system of trust.
- Control Privileges – One of the best practices to stay secure is to avoid using a root user in a container image. A user within containers must have the least privileges for system operation.
Running Containers
There are tools like Twistlock, Sysdig, Aqua, etc that offer threat prevention by monitoring network and system calls. Also, they are capable of intercepting and blocking unwanted calls to enforce security within the system.
These are the cloud container security checklist which developers must follow to build application quickly without any risk of cyber attacks.
Read more: Kubernetes vs Docker Swarm
4. Securing Applications

After ensuring the security of the infrastructure, Containers, Kubernetes installation process, the enterprise needs to focus on the security of the Application itself. Let’s find out how what include under this Kubernetes security checklist –
Application Access
- TLS for Kubernetes Ingress – The most well-known practice for presenting your application outside of the cluster is utilizing an ingress controller like Envoy or NGINX. All external access to the ingress controller should be over TLS, and interaction between the ingress controller and application containers must utilize TLS too, despite the fact that there are situations where that isn’t required – relying upon the organization plan and corporate security policies.
- Encrypt everything in Transit – Except for a couple of cases, the default behavior ought to encrypt everything in transit. It is prudent to encrypt network traffic between containers.
Communication
- Networking: Service networks like Istio, Linkerd, and Consul give many Layer 7 networking features, permitting the limitation and control of traffic between various tenants.
- Ports: It’s critical to just uncover the ports on your application/containers that are significant for communication to that application.
Application hardening
- Analyse and evaluate source code on regular basis to guarantee it is following all the norms to avoid vulnerabilities and threats.
- In general, developers depend on third-party applications and libraries to build their own applications and microservices. Therefore, it becomes of utmost importance to consistently examining code conditions for new vulnerabilities to guarantee that they are not a threat to the
- Constantly testing applications against common attacks like DDoS attacks, SQL injection etc.
Do you think Kubernetes will remain massively important to organizations after ten years from now? Of course, it will be. It is the safest and quickest way to deploy cloud native applications. If you are developing cloud native apps with this approach, do follow the Kubernetes security guidelinesand Cloud container security checklist for faster deployment in a safe environment.
Hire Kubernetes Experts in 48 hours
Are you looking for cyber security engineers having expertise in Kubernetes? Well, Peoplactive can help you hire cybers security experts within 48 hours of submitting the requisition. We maintain a pre-vetted talentpool of skilled and highly experienced candidates who are looking to assist you remotely on your project. Come and leverage our strong community of 4000+ candidates across the world.